Managing customer accounts across multiple digital touchpoints is one of the most challenging aspects of modern customer identity management. When customers register, update their profiles, or request account deletion, these changes need to be reflected everywhere. SCIM offers a standardized solution to automate this process entirely.
Introduction: What is SCIM?
SCIM stands for System for Cross-domain Identity Management. It is an open standard protocol (defined in RFC 7643 and RFC 7644) designed to automate the exchange of user identity information between different systems.
In simple terms: SCIM is the automatic synchronization layer for user data. Instead of manually managing customer accounts across your app, shop, newsletter system, and other platforms, SCIM handles this automatically based on changes in your central identity system.
The Problem SCIM Solves
Without SCIM: Fragmented Customer Data
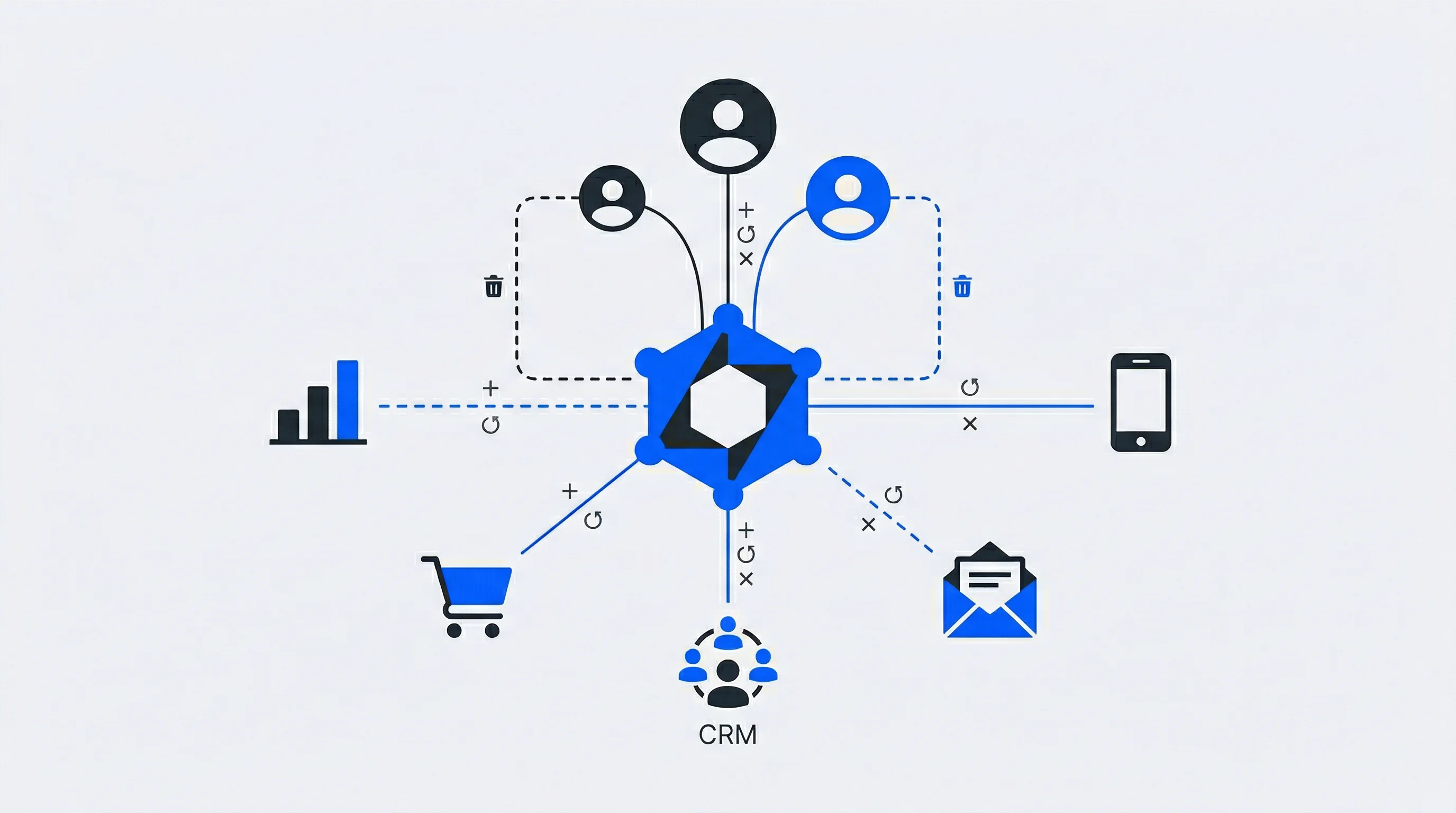
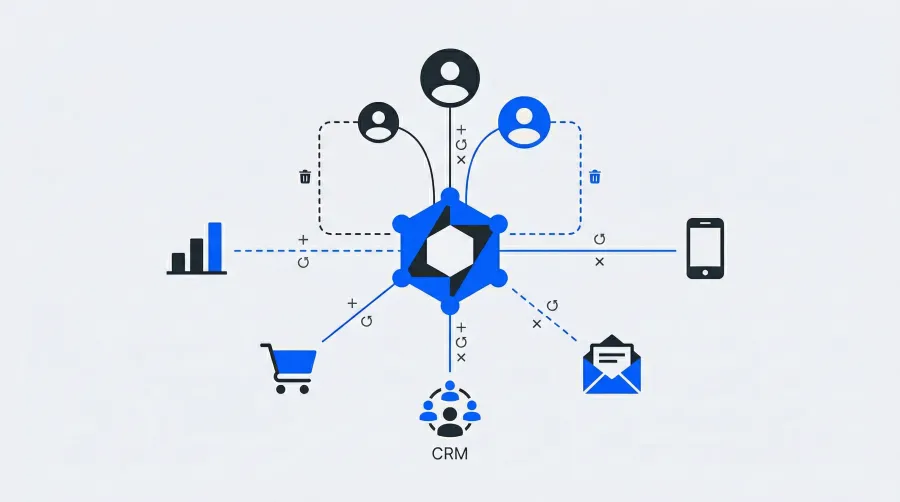
Consider what happens when a customer registers on your platform:
- Account is created in your identity system
- Customer data needs to sync to your newsletter tool
- Customer data needs to sync to your e-commerce platform
- Customer data needs to sync to your mobile app backend
- Customer data needs to sync to your CRM...
Without automation, this leads to data inconsistencies, delayed access, and frustrated customers. Worse still, when a customer requests data deletion under GDPR, you need to ensure removal from every single system.
With SCIM: Automated Customer Lifecycle Management
With SCIM in place:
- Customer registers once through your identity platform
- SCIM automatically provisions their profile to all connected applications
- Customer has immediate access across all your digital touchpoints
- Profile updates sync everywhere in real-time
- Account deletion: one action removes data from all systems
How SCIM Works
SCIM operates on a simple but powerful architecture:
┌─────────────────────────────────────────────────────────────┐
│ Identity Provider (SCIM Server) │
│ Single Source of Truth │
└─────────────────────────────────────────────────────────────┘
│ │ │ │
▼ ▼ ▼ ▼
┌─────────┐ ┌─────────┐ ┌─────────┐ ┌─────────┐
│ Shop │ │ App │ │Newsletter│ │ CRM │
└─────────┘ └─────────┘ └─────────┘ └─────────┘
All applications receive synchronized customer data automatically
The Three Core Functions
1. Provisioning (Create) When a new customer registers, SCIM automatically creates corresponding profiles in all connected applications with the appropriate data and permissions.
2. Synchronization (Update) When customer attributes change—such as email address, preferences, or consent settings—SCIM propagates these changes to all connected systems, ensuring data consistency.
3. Deprovisioning (Delete/Deactivate) When a customer deletes their account or revokes consent, SCIM automatically removes or anonymizes their data across all applications—critical for GDPR compliance.
Technical Foundation
SCIM is built on modern, widely-adopted technologies:
- REST API: Simple HTTP calls (GET, POST, PUT, PATCH, DELETE)
- JSON: Standardized data format for user and group objects
- Defined Schema: Consistent structure for attributes like name, email, and preferences
This means any SCIM-compliant system can communicate with any other SCIM-compliant system without custom integration work.
Standard User Attributes
SCIM defines a core schema for user objects:
| Attribute | Description |
|---|---|
userName | Unique identifier (often email) |
name | Given name, family name, display name |
emails | Email addresses |
groups | Segment or group memberships |
active | Account status |
locale | Language preference |
Organizations can extend this schema with custom attributes—such as marketing preferences, loyalty status, or consent flags.
SCIM and the Modern Identity Protocol Ecosystem
Understanding where SCIM fits within the broader landscape of identity protocols is crucial for building secure web applications. Each protocol serves a specific purpose in the identity management stack:
Core Identity Protocols Comparison
| Protocol | Primary Function | Best Use Case | Security Strength |
|---|---|---|---|
| OpenID Connect | Authentication | Single Sign-On for web/mobile apps | High (JWT tokens, PKCE) |
| SAML 2.0 | Authentication | Enterprise SSO, legacy systems | High (XML signing, encryption) |
| OAuth 2.0 | Authorization | API access, third-party integrations | High (token-based, scoped access) |
| SCIM 2.0 | User provisioning | Automated account lifecycle management | High (REST over HTTPS, bearer tokens) |
| LDAP | Directory services | Internal user directories | Medium (network-dependent) |
How Protocols Work Together
Modern secure web applications typically combine multiple protocols for comprehensive identity management:
OpenID Connect + SCIM: OpenID Connect handles customer authentication (how they log in), while SCIM manages account provisioning (ensuring accounts exist across all systems). This combination is ideal for customer-facing applications with multiple touchpoints.
SAML + SCIM: SAML provides enterprise-grade SSO for business applications, while SCIM automates employee account management across integrated systems. Common in B2B platforms serving enterprise customers.
OAuth + SCIM: OAuth manages API access permissions, while SCIM ensures user accounts are properly provisioned in systems that OAuth protects. Essential for API-driven architectures.
Choosing the Right Protocol Combination
Which combination is best suited for your business depends on your specific requirements:
- B2C Applications: OpenID Connect for authentication + SCIM for provisioning provides the best customer experience with automatic account management
- Enterprise Platforms: SAML for SSO + SCIM for provisioning ensures compatibility with corporate identity systems
- API-First Architectures: OAuth for authorization + SCIM for provisioning enables scalable, secure API access with proper account management
- Hybrid Environments: Support multiple protocols (OpenID Connect, SAML, OAuth) with SCIM as the common provisioning layer
The key insight: SCIM complements rather than competes with authentication protocols. While protocols like OpenID Connect and SAML handle the "how" of customer login, SCIM handles the "what" of account existence and data synchronization.
Business Benefits for Customer Identity
Seamless Customer Experience
Customers expect their data to be consistent across all touchpoints. With SCIM, a profile update in your app immediately reflects in your shop, newsletter preferences, and everywhere else. No more asking customers to update their information multiple times.
Faster Time-to-Value
When customers register, they expect immediate access. SCIM eliminates delays by instantly provisioning accounts across all your digital services. This reduces friction and improves conversion rates.
GDPR Compliance Made Simple
SCIM directly supports key GDPR requirements:
- Right to erasure: One deletion request removes data from all connected systems
- Data accuracy: Automatic synchronization ensures consistent, up-to-date information
- Consent management: Propagate consent changes across your entire tech stack
Reduced Operational Overhead
Manual data synchronization between systems is time-consuming and error-prone. SCIM automates this entirely, freeing your team to focus on customer experience rather than data management.
Better Data Quality
When customer data lives in multiple systems without synchronization, inconsistencies are inevitable. SCIM ensures a single source of truth, improving the quality of your customer insights and marketing effectiveness.
SCIM vs. SSO: Understanding the Difference
A common question is how SCIM relates to Single Sign-On (SSO). They serve different but complementary purposes:
| Aspect | SSO (Single Sign-On) | SCIM |
|---|---|---|
| Purpose | How customers authenticate | Whether accounts exist |
| Function | One login for all platforms | Automated account management |
| Timing | At every login | When customer data changes |
| Analogy | A universal key | Automatic key management |
Both work together: SSO provides seamless authentication across your digital ecosystem, while SCIM ensures customer accounts exist and are properly configured in the first place.
Implementation Considerations
Common Integration Scenarios
SCIM is particularly valuable for organizations with multiple customer-facing systems:
- E-commerce platforms: Shopify, Shopware, WooCommerce
- Email marketing: Mailchimp, Klaviyo, HubSpot — or your own newsletter subscription system
- Customer support: Zendesk, Intercom
- Mobile apps: Custom app backends
- Analytics: Customer data platforms
Selecting Identity Management Platforms for SCIM Integration
When evaluating identity management platforms for SCIM implementation, consider both the platform's core capabilities and how well they support your customer identity orchestration needs:
Enterprise-Focused Platforms
- Okta: Comprehensive SCIM support with extensive app catalog, but primarily enterprise-focused with complex pricing for customer identity use cases
- Microsoft Entra ID: Strong SCIM capabilities and Azure ecosystem integration, though can be overengineered for customer-facing applications
- Ping Identity: Robust enterprise identity features with SCIM support, but typically requires significant implementation expertise
Developer-Friendly Platforms
- Auth0: Good SCIM support with flexible API-first approach, though custom development often required for complex provisioning workflows
- FusionAuth: Open-source with SCIM capabilities, requires more hands-on configuration but offers deployment flexibility
- Amazon Cognito: Basic user provisioning through APIs, though lacks full SCIM standard compliance
Customer Identity Specialized Platforms
For organizations prioritizing customer identity management, consider platforms specifically designed for customer-facing applications:
- Ready-to-go integration: Look for platforms offering 100+ pre-built integrations to avoid custom SCIM development
- Branded user experience: Ensure the platform supports fully branded customer account management interfaces
- Consent and compliance: Choose platforms with built-in GDPR compliance and consent management features
- Revenue features: Consider platforms that connect identity to digital sales growth through premium memberships and ID-based campaigns
Evaluation Criteria
When comparing identity orchestration tools for your specific needs, evaluate:
- Protocol support: Full compliance with SCIM 2.0, OpenID Connect, and SAML standards
- Integration depth: Number of pre-built connectors vs. custom development requirements
- Data synchronization: Real-time vs. batch processing capabilities
- Customization flexibility: Support for custom user attributes and provisioning workflows
- Monitoring and troubleshooting: Visibility into provisioning activities and failure handling
- Compliance features: Built-in support for GDPR, data residency, and audit logging
The right choice depends on whether you need a comprehensive customer identity platform or can integrate SCIM capabilities into your existing technical architecture.
Best Practices
- Start with systems that handle the most sensitive customer data
- Ensure proper consent management is in place before enabling sync
- Test thoroughly with a subset of users before full rollout
- Monitor synchronization activities and set up alerts for failures
- Document which data attributes are shared with each connected system
The Future of Customer Identity Provisioning
As organizations adopt more customer-facing applications and privacy regulations become stricter, automated identity provisioning becomes essential. Key trends include:
- Real-time sync: Event-driven provisioning via webhooks for instant updates
- Privacy-first design: Built-in consent propagation and data minimization
- Extended attributes: Support for custom customer segments and preferences
Conclusion
SCIM transforms customer identity management from a fragmented, manual process into an automated, consistent, and compliant system. By establishing a single source of truth for customer identities and automatically synchronizing that data across all connected applications, organizations can:
- ✅ Deliver seamless customer experiences across all touchpoints
- ✅ Ensure GDPR compliance with automated data lifecycle management
- ✅ Maintain consistent customer data quality
- ✅ Reduce operational overhead and manual errors
- ✅ Scale customer identity management effortlessly
Whether you're managing thousands or millions of customer identities, implementing SCIM is a foundational step toward modern, privacy-compliant customer identity management.
Want to learn more about implementing SCIM for your customer identity platform? Contact us for a consultation.
SAML vs. OIDC: Best Protocol for Your Business
What are SAML (Security Assertion Markup Language) and OIDC (OpenID Connect)? Both are authentication protocols that enable Single Sign-On (SSO). Which one is better suited for your business? We introduce both protocols, how they work, their features, and which one is best for your company.
Single Sign-On for Clubs: Why Member Login, Shop, Ticketing, and Newsletter Belong Together
Single Sign-On (SSO) is an authentication method that allows users to access multiple, independent applications with one set of credentials—logging in once to reach everything from a member portal to a shop, ticketing system, and newsletter without re-entering passwords.